Unlock the Secrets of G Network Security Measures: A Comprehensive Guide to Safeguarding Your Network
Understanding the Importance of Network Security Measures
In today's digital age, where data breaches and cyber threats are on the rise, it's more crucial than ever to implement robust network security measures. As part of our commitment to providing valuable insights into the latest security trends, we'll delve into the world of G Network Security Measures, exploring the essential controls, tools, and strategies that help protect your network from various threats. Whether you're a business owner, IT professional, or cybersecurity enthusiast, this article will provide you with actionable tips and knowledge to safeguard your online presence.Network Security Measures: Protecting Confidentiality, Integrity, and Availability
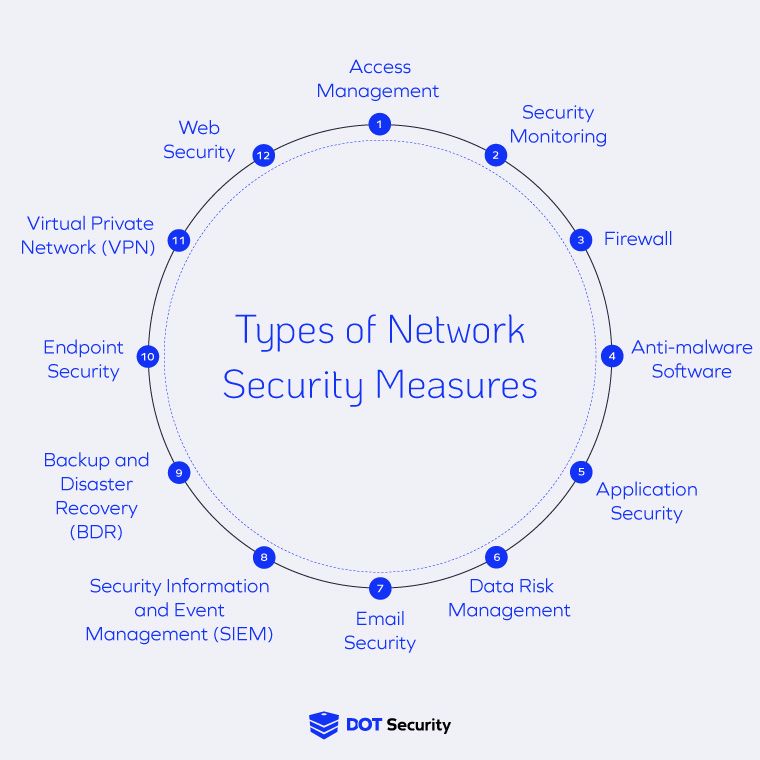
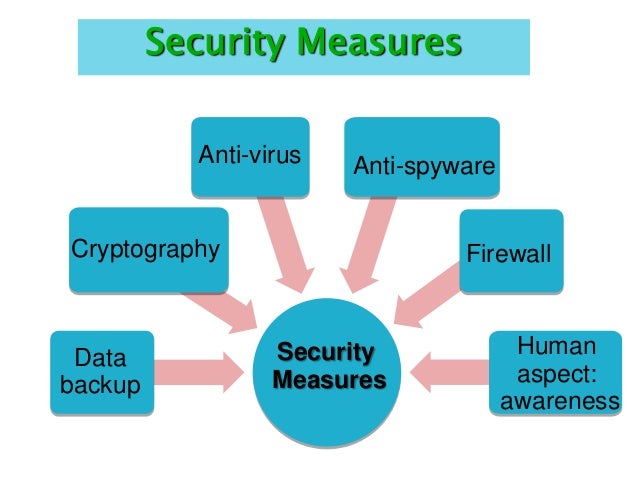
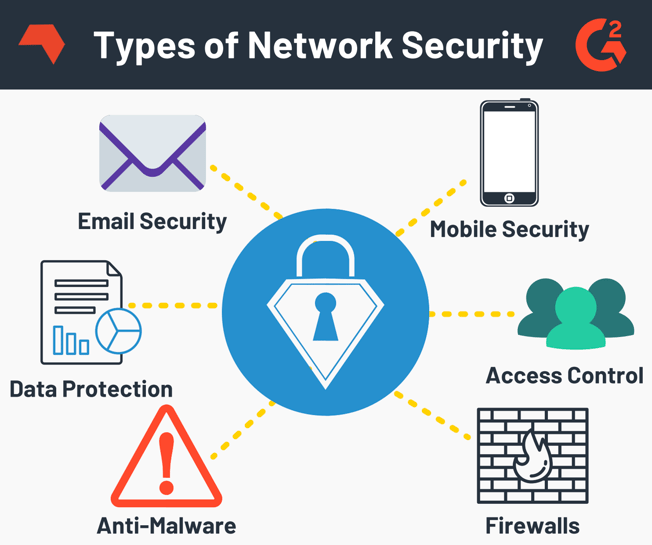
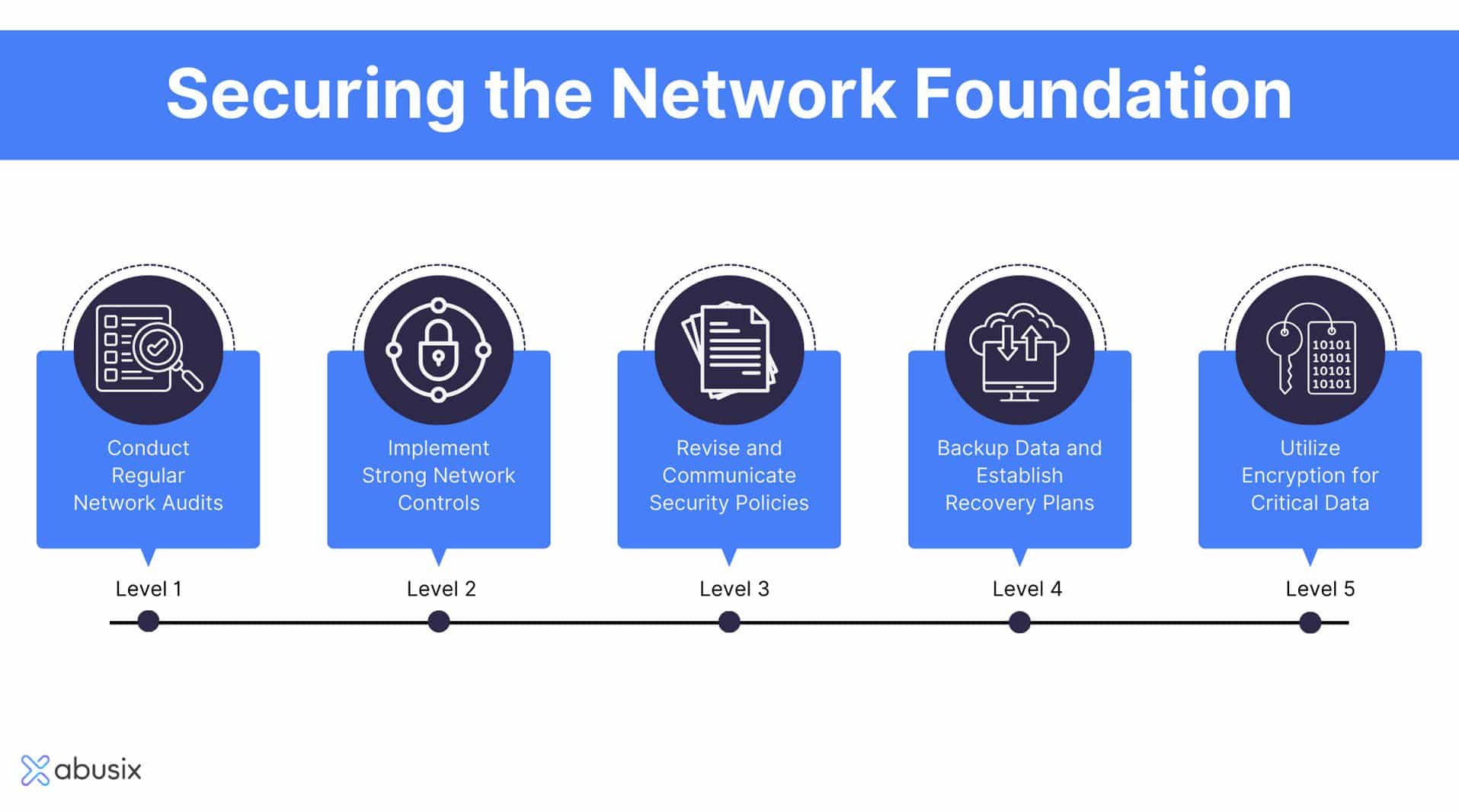
A well-protected network is the backbone of any organization, and network security measures play a pivotal role in maintaining the confidentiality, integrity, and availability of sensitive data. The following are some of the key security controls that can be implemented to safeguard your network:Access Control: The First Line of Defense
Access control is the foundation of any robust network security strategy. It involves implementing measures such as: * Multi-factor authentication: This adds an extra layer of security by requiring users to provide a second form of verification in addition to a password. * Role-Based Access Control (RBAC): This grants or denies access to network resources based on a user's role or position within the organization. * Identity and Access Management (IAM): This ensures that users have the necessary permissions to access specific resources, reducing the risk of unauthorized access.Antivirus and Malware Protection
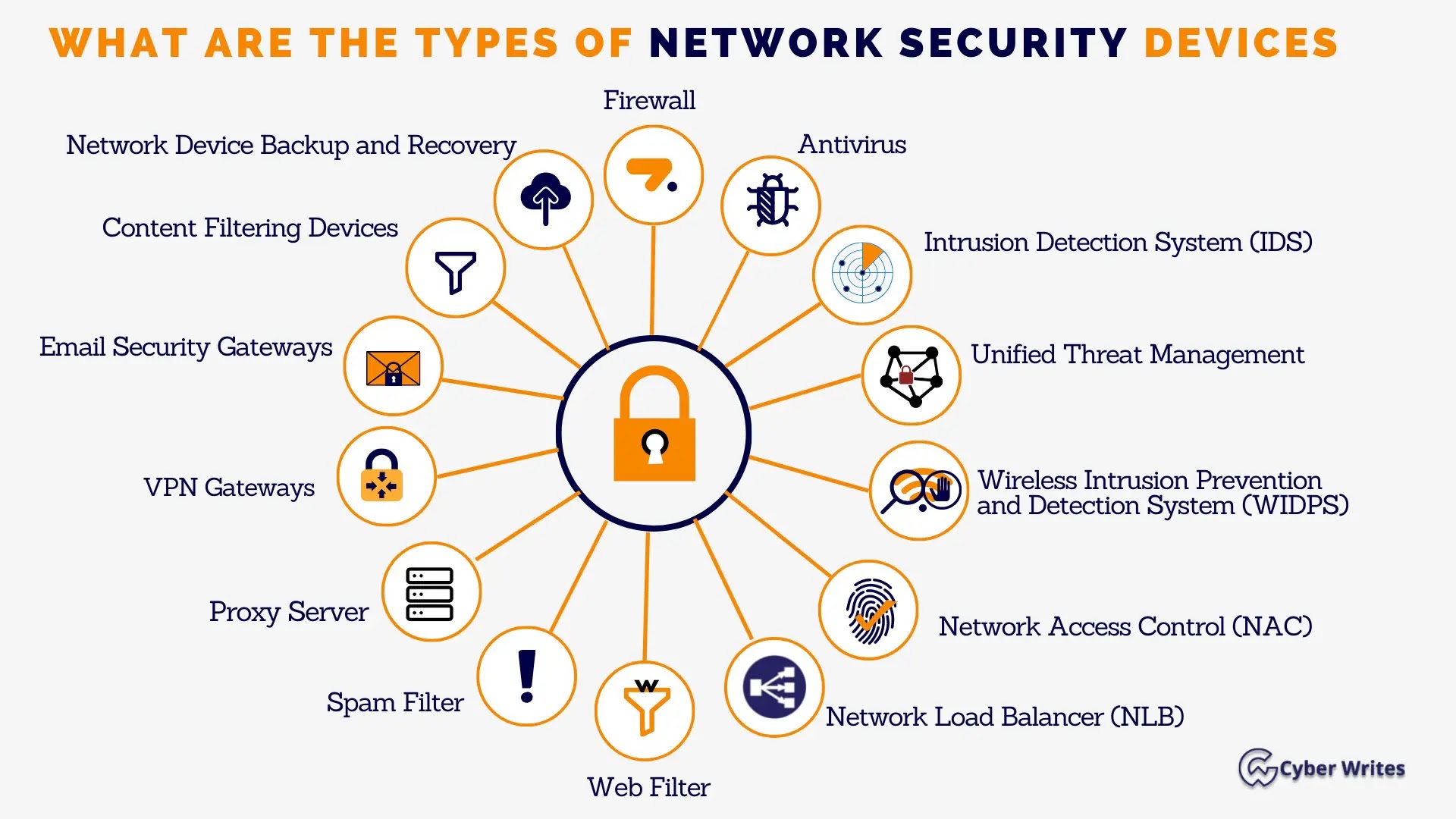
To prevent malware and viruses from infiltrating your network, implement robust antivirus and malware protection measures, including: * Installing up-to-date antivirus software that detects and eliminates malware and viruses. * Regularly updating operating systems and software to ensure the latest security patches are applied. * Implementing intrusion detection and prevention systems to detect and block malicious activity.Firewalls and Network Segmentation