Setting Up a G Network for Secure File Transfer
In today's digital age, secure file transfer has become a top priority for individuals and organizations alike. With the increasing amount of sensitive data being shared over networks, it's essential to have a robust and secure method for transferring files. One way to achieve this is by setting up a G network for secure file transfer.
Understanding the Importance of Secure File Transfer
Secure file transfer is crucial for several reasons. Firstly, it protects sensitive data from unauthorized access, reducing the risk of data breaches and cyber attacks. Secondly, it ensures compliance with regulatory requirements, such as GDPR and HIPAA, which demand secure data handling practices. Lastly, it builds trust among stakeholders, including customers, partners, and employees.
Benefits of Setting Up a G Network for Secure File Transfer
A G network for secure file transfer offers numerous benefits, including:
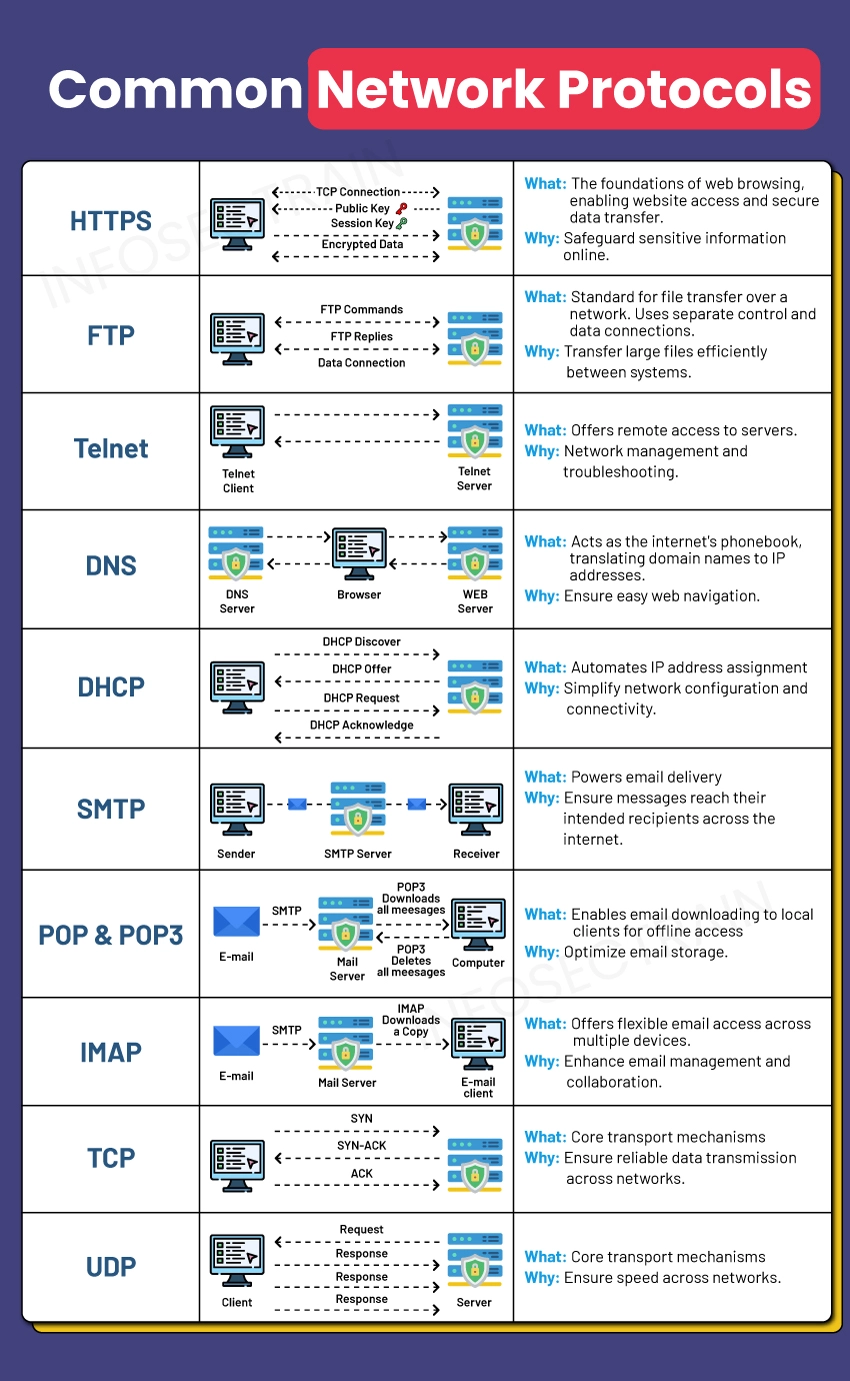
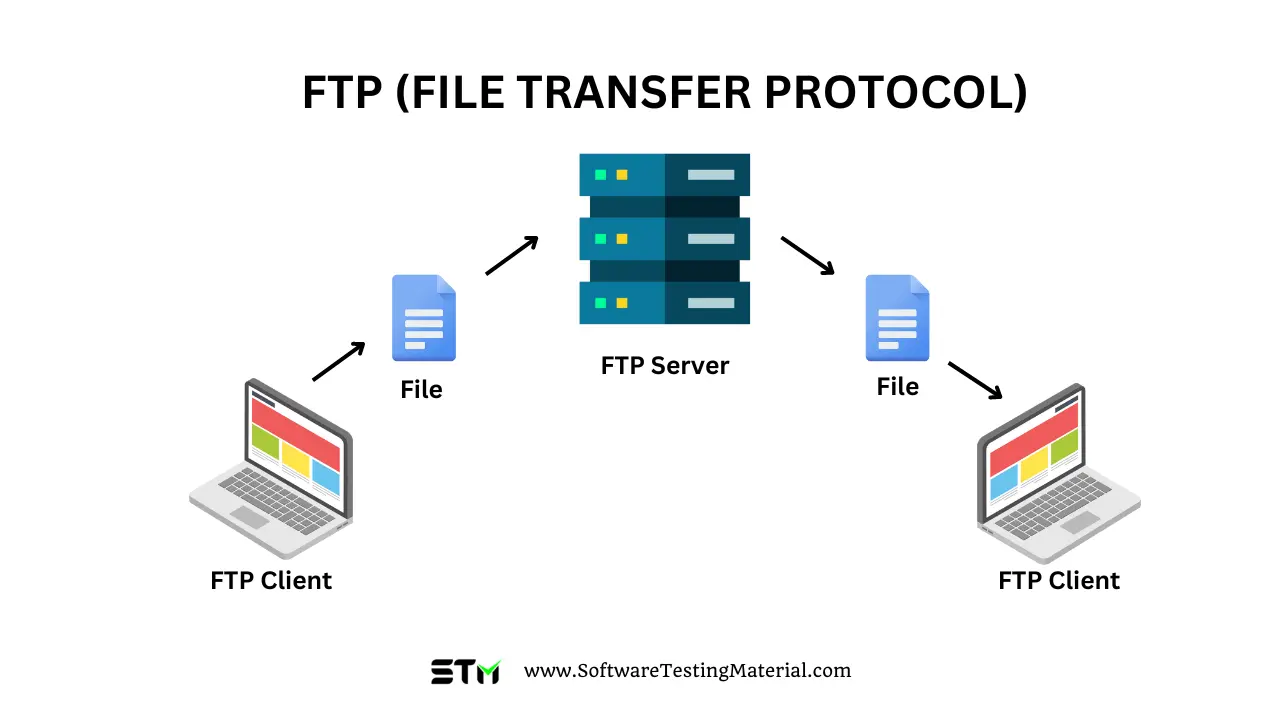
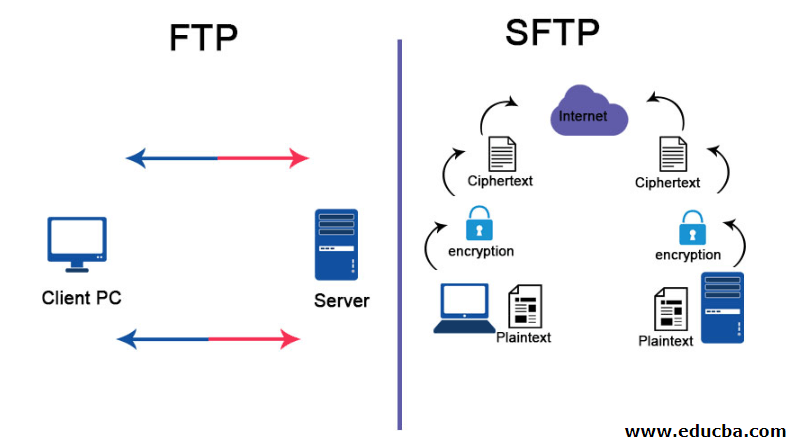
- Enhanced security: G networks use advanced encryption protocols, such as SFTP and SCP, to ensure secure data transfer.
- Improved compliance: By adhering to regulatory requirements, organizations can avoid fines and penalties associated with data breaches.
- Increased productivity: Secure file transfer enables efficient collaboration and data sharing, boosting productivity and reducing administrative burdens.
- Scalability: G networks can handle large volumes of data transfer, making them ideal for organizations with complex data management needs.
Steps to Set Up a G Network for Secure File Transfer
To set up a G network for secure file transfer, follow these steps:
- Choose a secure file transfer protocol: Select a protocol that meets your organization's security requirements, such as SFTP, SCP, or FTPS.
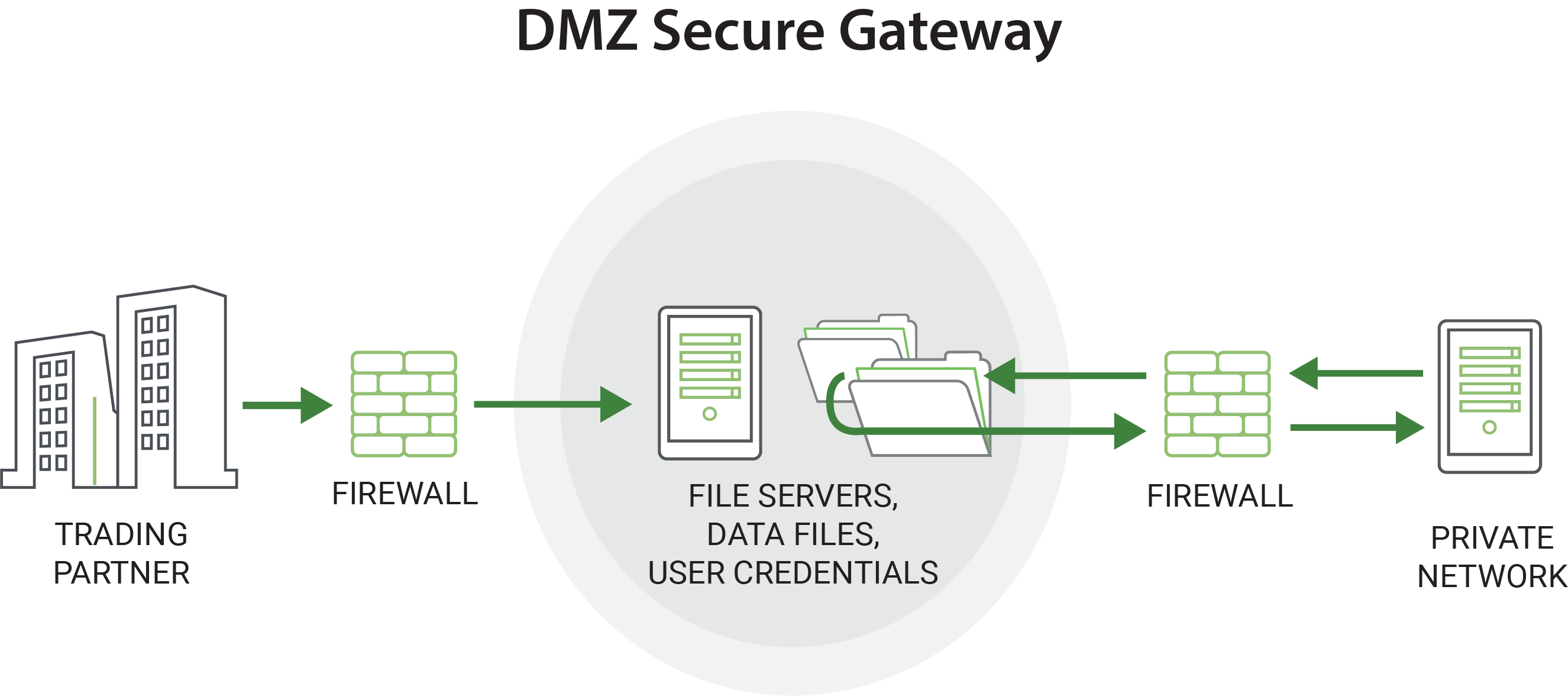
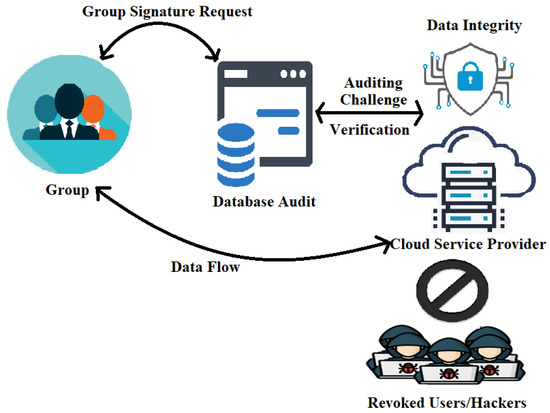
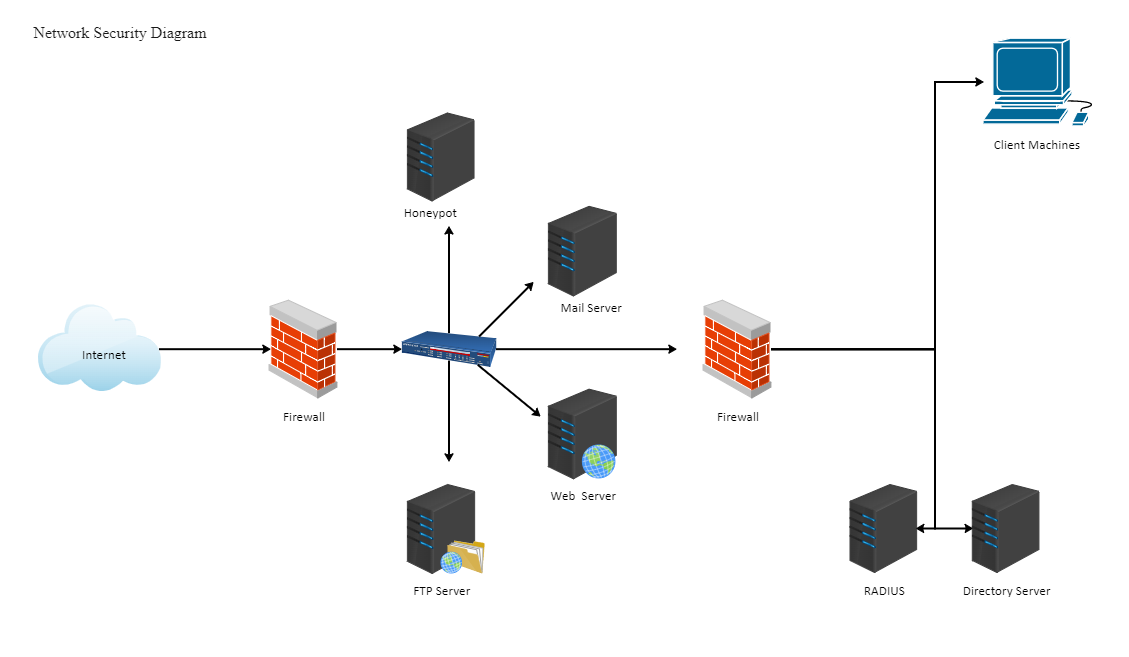
- Set up a G network: Establish a G network by creating a virtual private network (VPN) or using a cloud-based service, such as AWS Transfer Family.
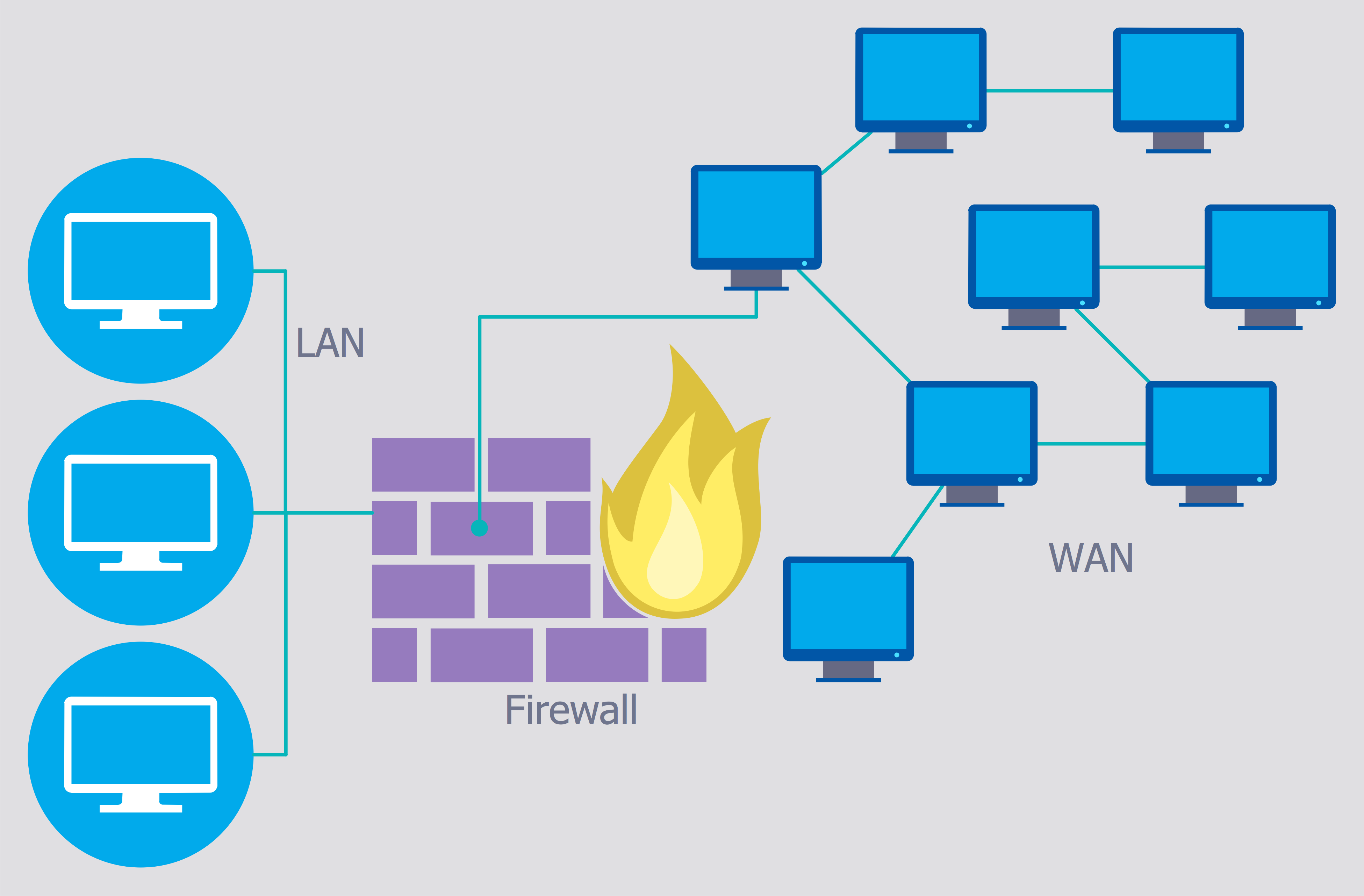
- Configure security settings: Implement security settings, including firewalls, intrusion detection systems, and access controls, to protect your G network.
- Test and validate: Test your G network for secure file transfer to ensure it meets your organization's security requirements.
- Monitor and maintain: Regularly monitor your G network for secure file transfer and maintain it to ensure it remains secure and compliant.
Conclusion
Setting up a G network for secure file transfer is a crucial step in protecting sensitive data and ensuring compliance with regulatory requirements. By following the steps outlined in this article, organizations can establish a secure and efficient file transfer process that meets their needs.
Additional Tips and Considerations
When setting up a G network for secure file transfer, consider the following additional tips and considerations:
- Implement user education and training: Educate users on secure file transfer practices and the importance of data protection.
- Regularly update security settings: Regularly update security settings to ensure they remain effective against evolving threats.
- Monitor network activity: Monitor network activity to detect potential security threats and anomalies.
- Use secure file transfer tools: Utilize secure file transfer tools, such as AWS Transfer Family, to simplify and secure file transfer processes.