Configuring Your G Wireless Router for Secure File Transfer
With the increasing need for secure and efficient file transfer, configuring your G wireless router is a crucial step in ensuring the security and integrity of your network. In this article, we will guide you through the process of configuring your G wireless router for secure file transfer, providing you with a comprehensive understanding of the key settings and features to secure your network.
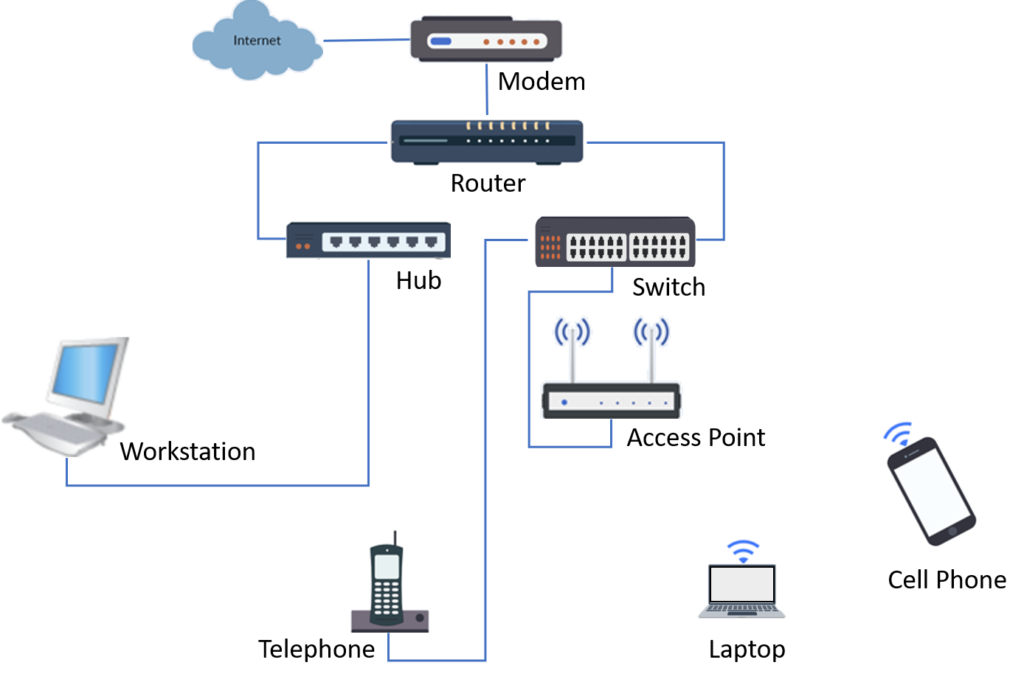
Understanding Your G Wireless Router
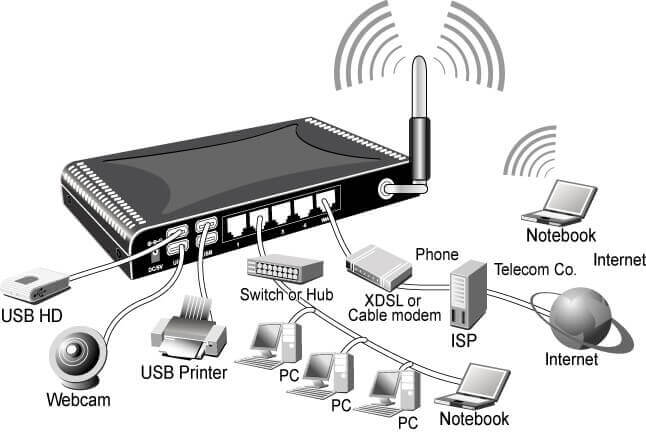
Your G wireless router is a vital component of your home network, allowing you to access the internet and share files with ease. With its advanced security features and user-friendly interface, configuring your router is a straightforward process that can be completed in a few simple steps.
Configuring Your Router for Secure File Transfer
To configure your router for secure file transfer, follow these steps:
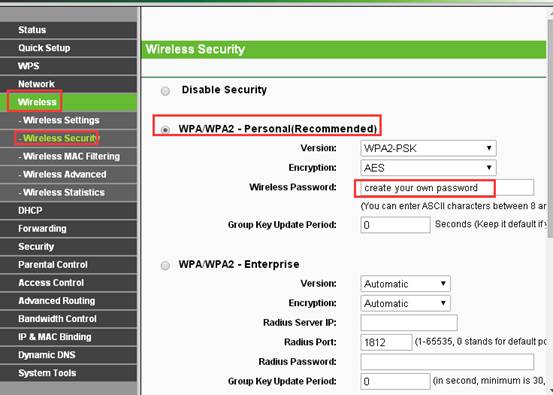
- Change the Default Administrator Password: The default administrator password is usually found on the bottom or back of your router. Change this password to a strong and unique one to prevent unauthorized access.
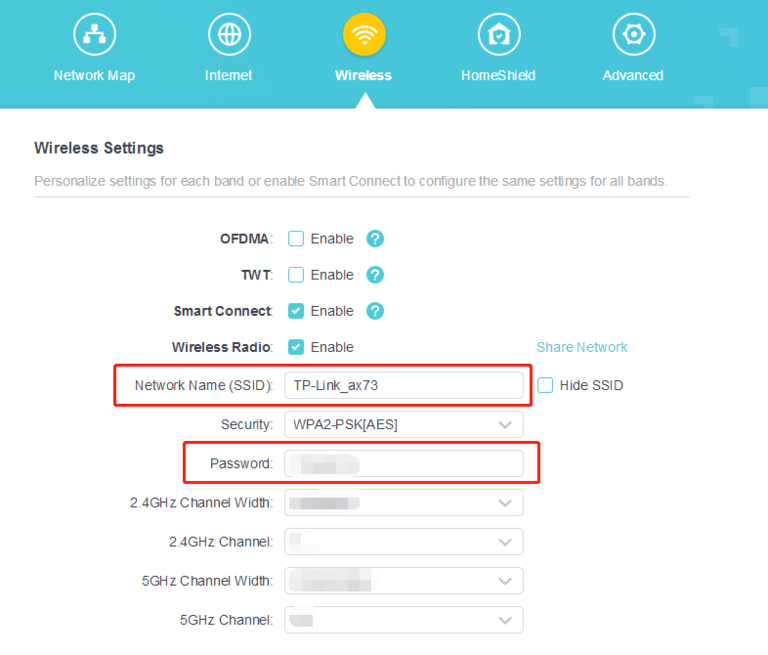
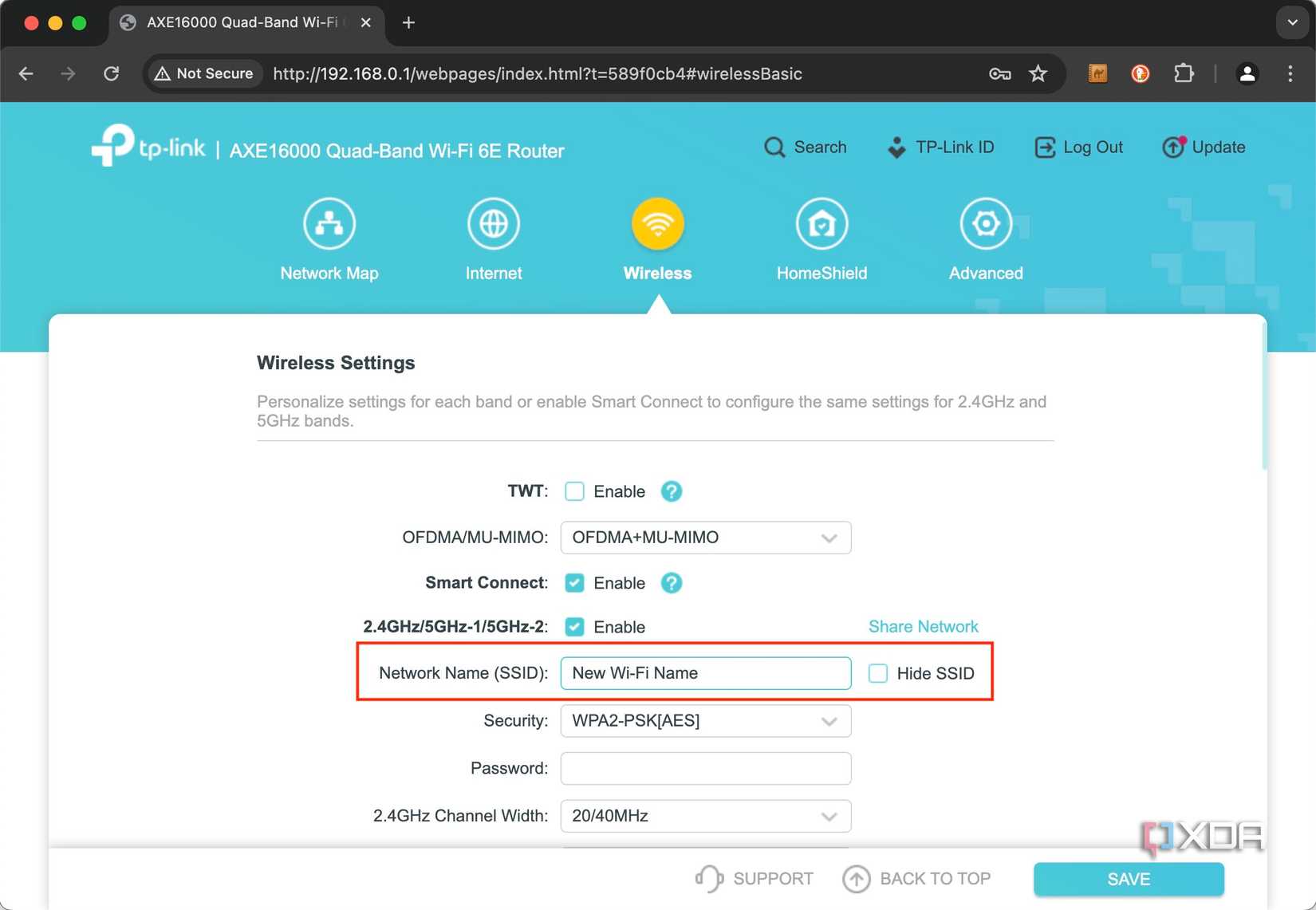
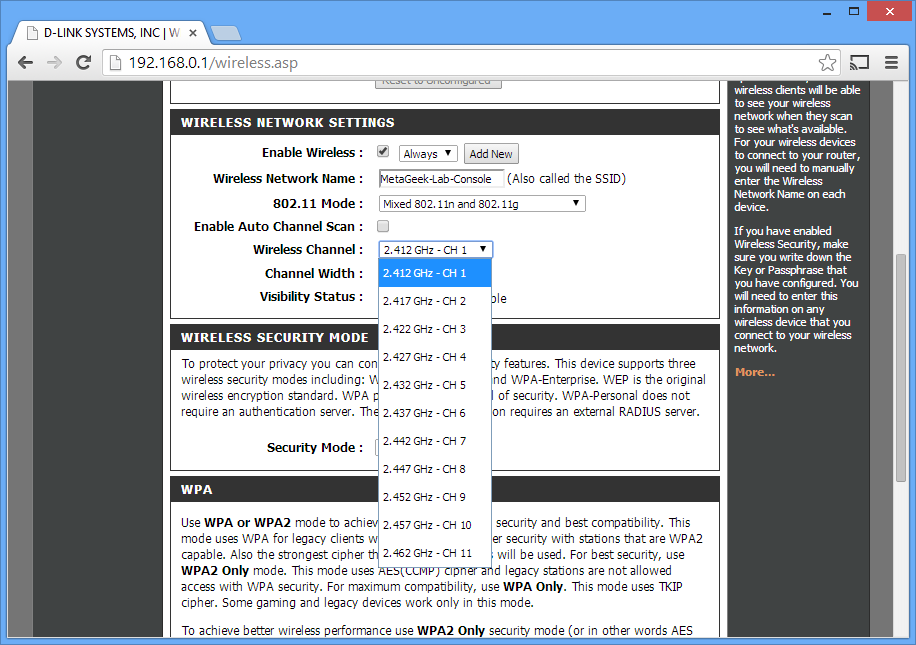
- Enable WPA2 Encryption: WPA2 is the most secure encryption protocol available for wireless networks. Enable WPA2 encryption on your router to ensure that all data transmitted over your network is secure.
- Set Up a Guest Network: A guest network allows visitors to access the internet without compromising the security of your main network. Set up a guest network on your router to provide a separate and secure connection for guests.
- Update Your Router's Firmware: Regularly update your router's firmware to ensure that you have the latest security patches and features.
- Configure Your Router's Firewall: Your router's firewall helps to block unauthorized access to your network. Configure your firewall to allow only necessary traffic and block all other incoming and outgoing traffic.
Additional Security Measures
While configuring your router for secure file transfer is a crucial step, there are additional security measures you can take to further protect your network:
- Use a VPN: A virtual private network (VPN) encrypts your internet traffic, making it difficult for hackers to intercept your data.
- Implement Two-Factor Authentication: Two-factor authentication requires users to provide a second form of verification, such as a code sent to their phone, in addition to their password.
- Regularly Back Up Your Data: Regularly back up your important files and data to an external hard drive or cloud storage service to prevent data loss in case of a security breach.
Conclusion
Configuring your G wireless router for secure file transfer is a crucial step in ensuring the security and integrity of your network. By following the steps outlined in this article and implementing additional security measures, you can protect your network from unauthorized access and ensure the secure transfer of files.
Recommended Resources
For more information on configuring your G wireless router and implementing additional security measures, we recommend the following resources:
- Belkin G Wireless Router User Manual: View and download the user manual for your Belkin G wireless router online.
- Linksys Wireless-G Broadband Router User Manual: View and download the user manual for your Linksys Wireless-G Broadband Router online.
- TP-Link Wireless Router Support: Visit the TP-Link website for support and resources on configuring your wireless router.
Final Thoughts
Configuring your G wireless router for secure file transfer is a straightforward process that requires minimal technical expertise. By following the steps outlined in this article and implementing additional security measures, you can protect your network from unauthorized access and ensure the secure transfer of files. Remember to regularly update your router's firmware, configure your firewall, and implement additional security measures to maintain the security and integrity of your network.