G Network Configuration for Network Segmentation: A Comprehensive Guide
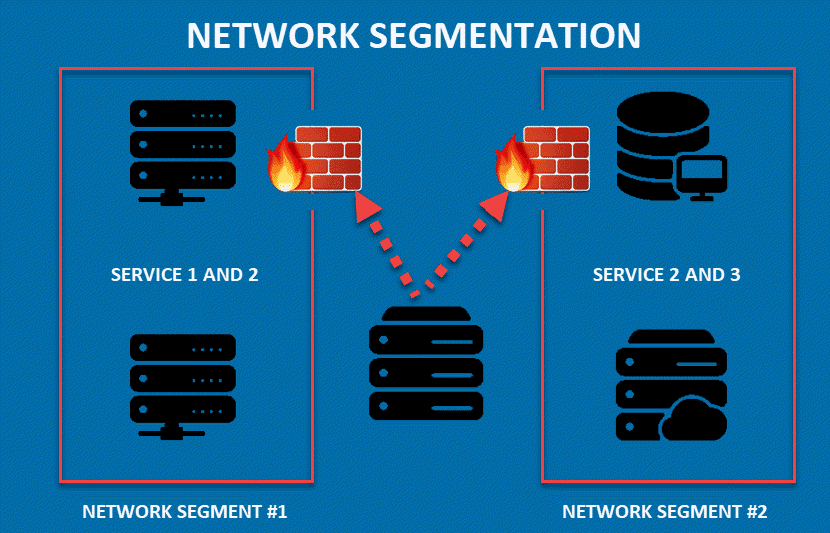
Network segmentation is a crucial security measure that involves dividing a network into smaller, isolated segments or subnets to limit access, contain potential threats, and enhance security and performance. A well-configured network segmentation strategy can help organizations improve their security posture, reduce the spread of cyberattacks, and enhance compliance. In this article, we will explore the concept of G Network Configuration for Network Segmentation and provide a comprehensive guide on how to implement it effectively.
What is G Network Configuration for Network Segmentation?
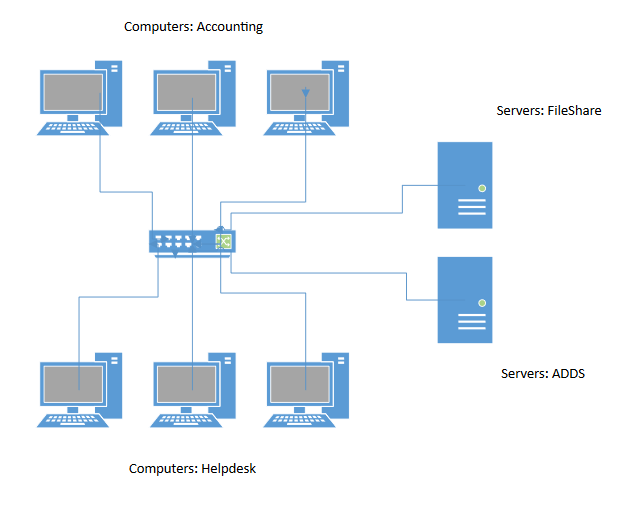
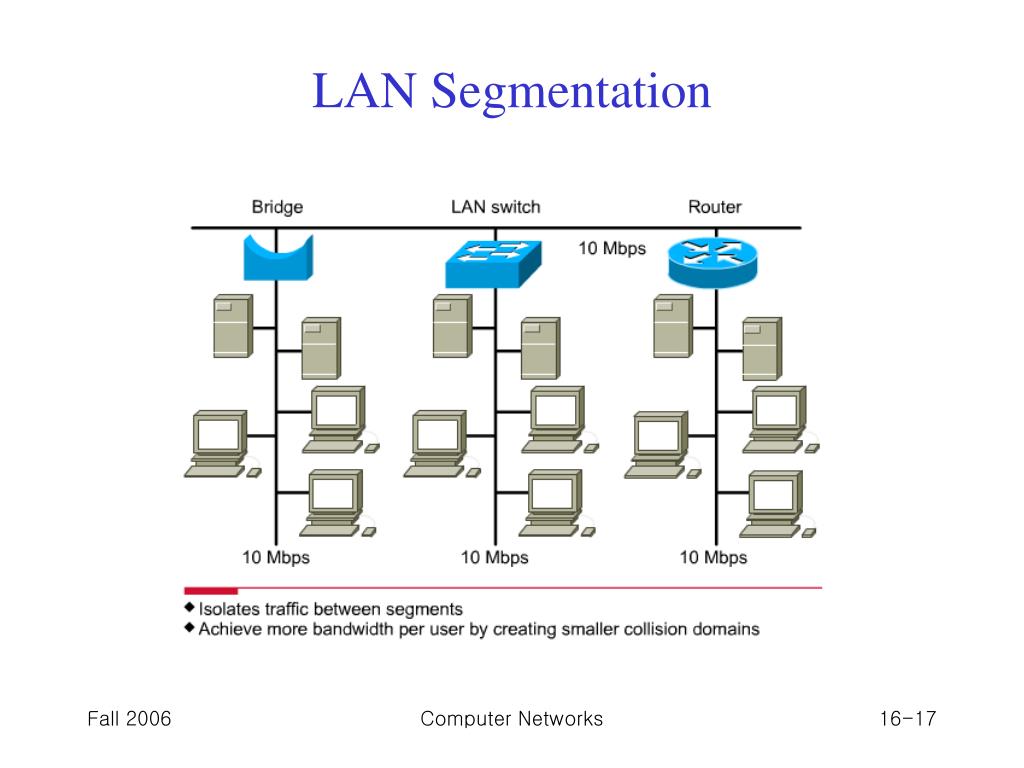
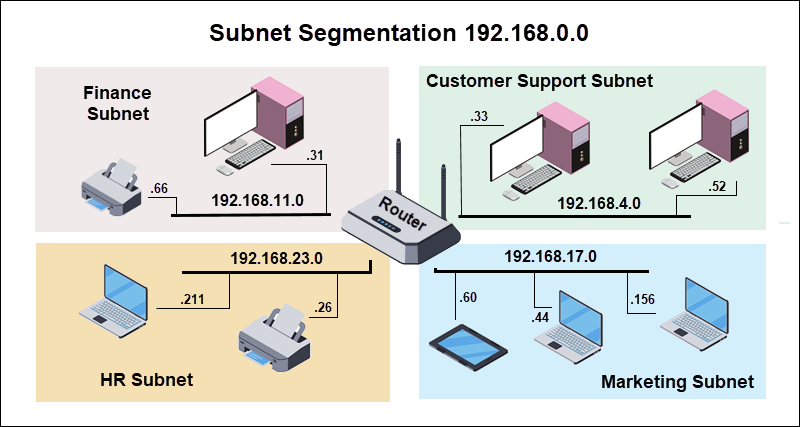
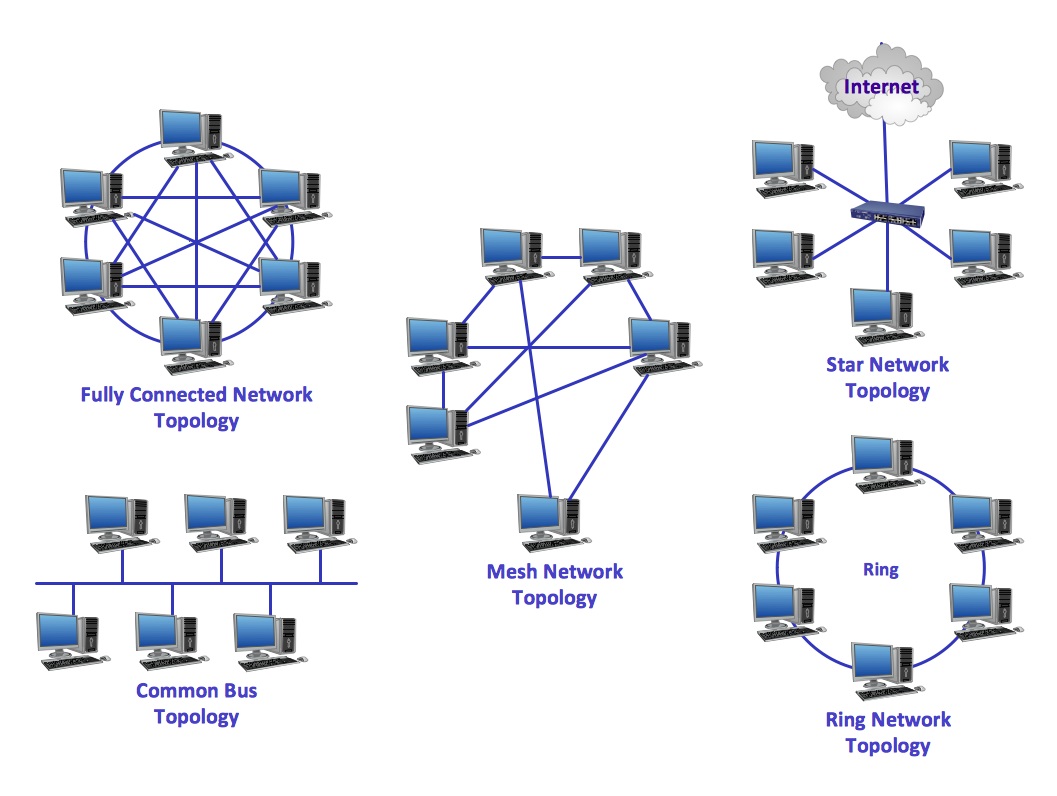
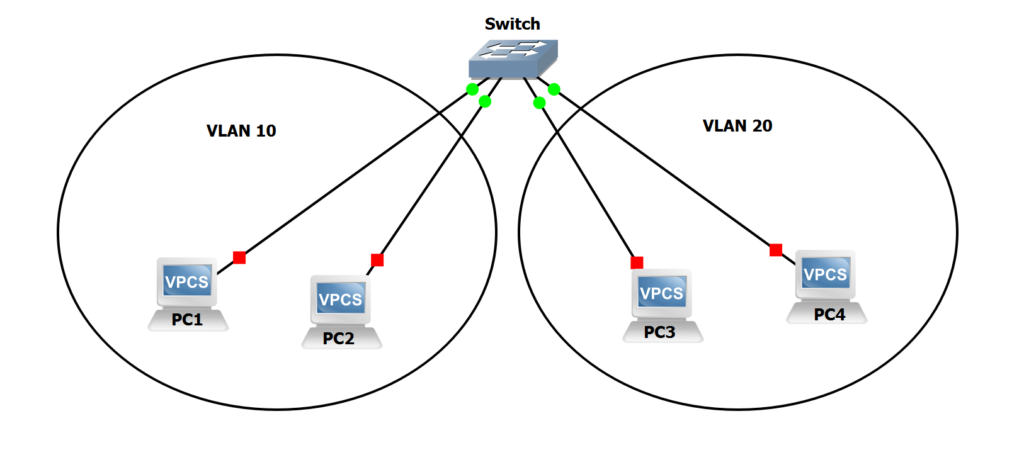
G Network Configuration for Network Segmentation refers to the process of designing and implementing a network architecture that divides a large network into smaller, isolated segments or subnets. This involves configuring the network devices, such as routers, switches, and firewalls, to control the flow of network traffic between segments and enforce granular policies. The goal of G Network Configuration for Network Segmentation is to create a secure and isolated environment for each segment, thereby reducing the attack surface and improving overall security.
Benefits of G Network Configuration for Network Segmentation
The benefits of G Network Configuration for Network Segmentation are numerous. Some of the key advantages include:
- Improved Security**: Network segmentation can help reduce the attack surface by isolating sensitive areas of the network, making it more difficult for attackers to access and exploit vulnerable systems.
- Enhanced Performance**: By dividing the network into smaller segments, organizations can improve network performance by reducing congestion and minimizing the impact of a security breach.
- Increased Compliance**: Network segmentation can help organizations comply with regulatory requirements, such as HIPAA, PCI-DSS, and GDPR, by isolating sensitive data and enforcing granular policies.
- Reduced Downtime**: In the event of a security breach or network failure, network segmentation can help isolate the affected segment, reducing downtime and minimizing the impact on business operations.
Design Principles for G Network Configuration for Network Segmentation
When designing a G Network Configuration for Network Segmentation, organizations should follow these key principles:
- Simplify and Segment**: Divide the network into smaller, isolated segments or subnets to improve security and performance.
- Granular Policies**: Enforce granular policies between segments to control the flow of network traffic and enforce security requirements.
- Network Isolation**: Isolate sensitive areas of the network, such as data centers, to reduce the attack surface and minimize the impact of a security breach.
- Monitoring and Maintenance**: Regularly monitor and maintain the network segmentation configuration to ensure it remains effective and up-to-date.

Configuring G Network for Network Segmentation
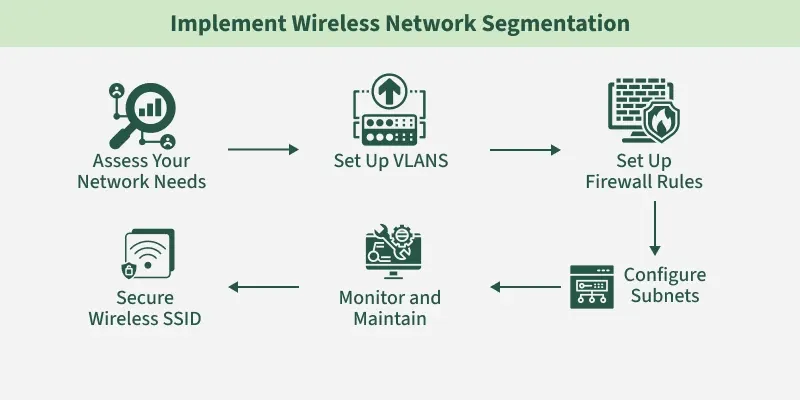
Configuring a G Network for Network Segmentation involves several steps, including:
- Identifying Segments**: Identify the different segments or subnets that will be created within the network.
- Configuring Devices**: Configure the network devices, such as routers, switches, and firewalls, to control the flow of network traffic between segments.
- Enforcing Policies**: Enforce granular policies between segments to control the flow of network traffic and enforce security requirements.
- Monitoring and Maintenance**: Regularly monitor and maintain the network segmentation configuration to ensure it remains effective and up-to-date.
Best Practices for G Network Configuration for Network Segmentation
To ensure the effectiveness of G Network Configuration for Network Segmentation, organizations should follow these best practices:
- Regularly Review and Update Configuration**: Regularly review and update the network segmentation configuration to ensure it remains effective and up-to-date.
- Use Granular Policies**: Use granular policies to control the flow of network traffic between segments and enforce security requirements.
- Monitor Network Traffic**: Monitor network traffic to detect and respond to security threats in a timely manner.
- Provide Training**: Provide training to network administrators and security personnel on the importance of network segmentation and how to configure it effectively.
Conclusion
In conclusion, G Network Configuration for Network Segmentation is a critical security measure that involves dividing a network into smaller, isolated segments or subnets to limit access, contain potential threats, and enhance security and performance. By following the design principles, configuring devices, enforcing policies, and monitoring and maintaining the network segmentation configuration, organizations can improve their security posture, reduce the spread of cyberattacks, and enhance compliance. Remember to regularly review and update the configuration, use granular policies, monitor network traffic, and provide training to network administrators and security personnel to ensure the effectiveness of G Network Configuration for Network Segmentation.