Setting Up a G Network for Data Encryption
In today's digital age, protecting data in transit has become a top priority for individuals and organizations alike. One effective way to ensure the confidentiality and integrity of your data is by implementing a Virtual Private Network (VPN) or a dedicated network with encryption protocols. This article will guide you through the process of setting up a G network for data encryption, ensuring your data remains secure and compliant with regulatory requirements.
Understanding Data Encryption
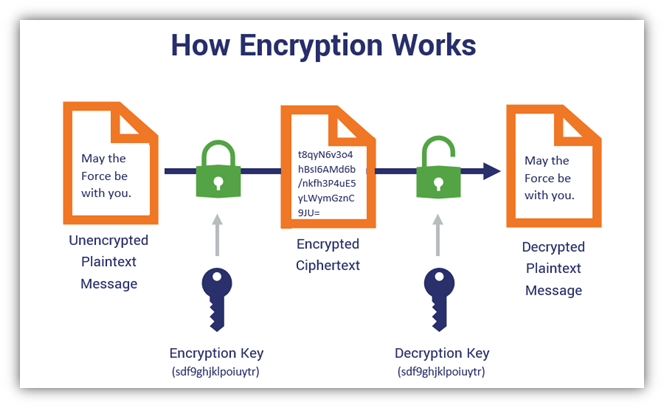
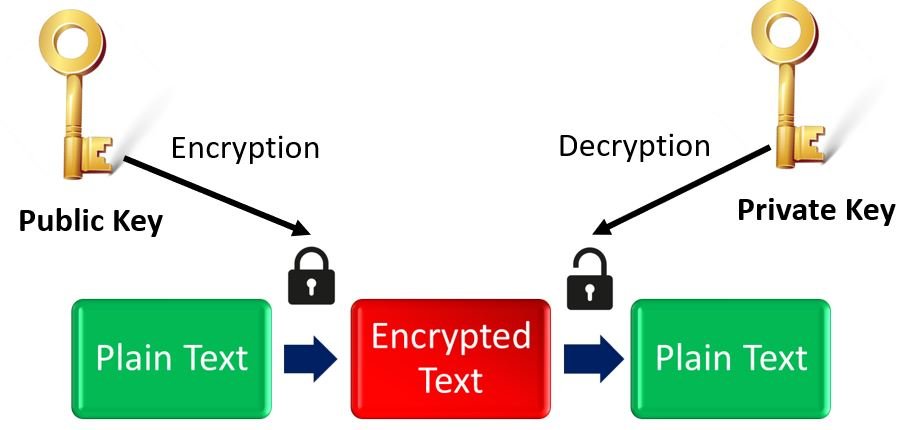
Before diving into the setup process, it's essential to understand the concept of data encryption. Data encryption involves converting sensitive information into an unreadable format using a cryptographic algorithm, protecting it from unauthorized access. This process requires a pair of keys: a public key for encryption and a private key for decryption.
Types of Encryption Algorithms
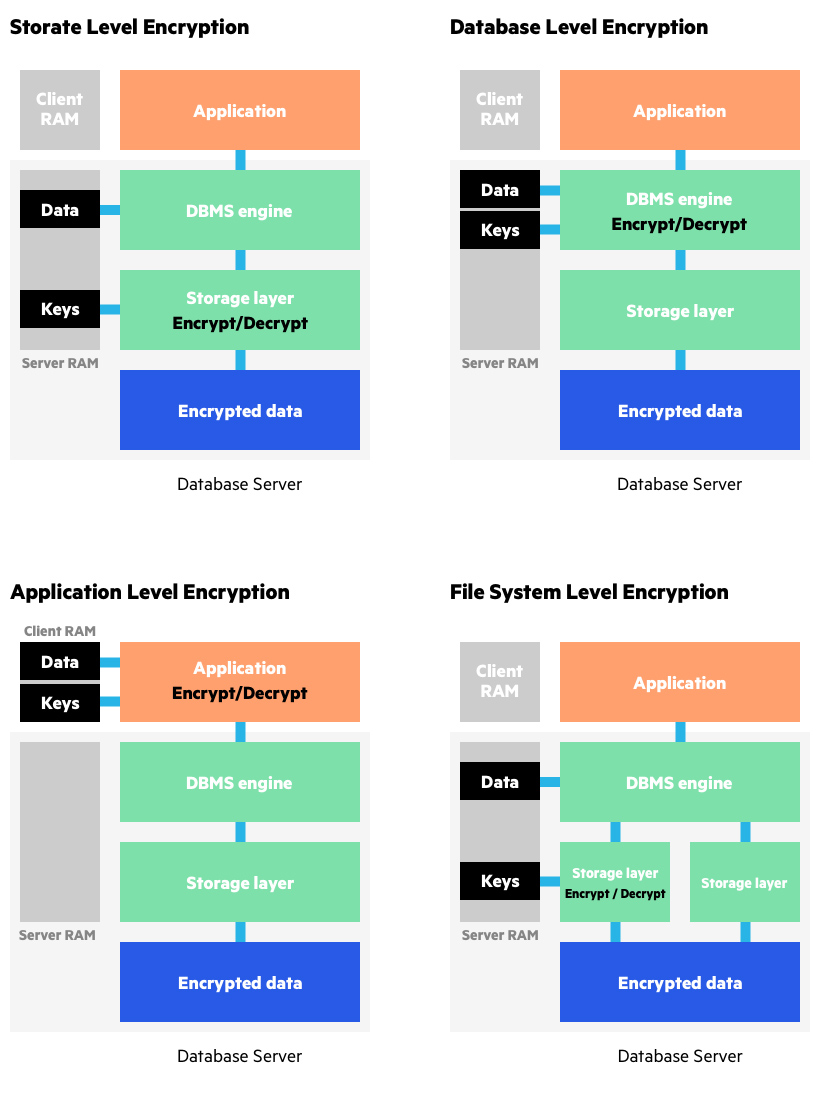
There are two primary types of encryption algorithms: symmetric and asymmetric. Symmetric encryption uses the same key for both encryption and decryption, while asymmetric encryption uses a pair of keys - a public key for encryption and a private key for decryption. Common symmetric algorithms include AES (Advanced Encryption Standard), a block cipher that operates on 128-bit blocks with key sizes of 128, 192, or 256 bits.
Setting Up a VPN or Dedicated Network
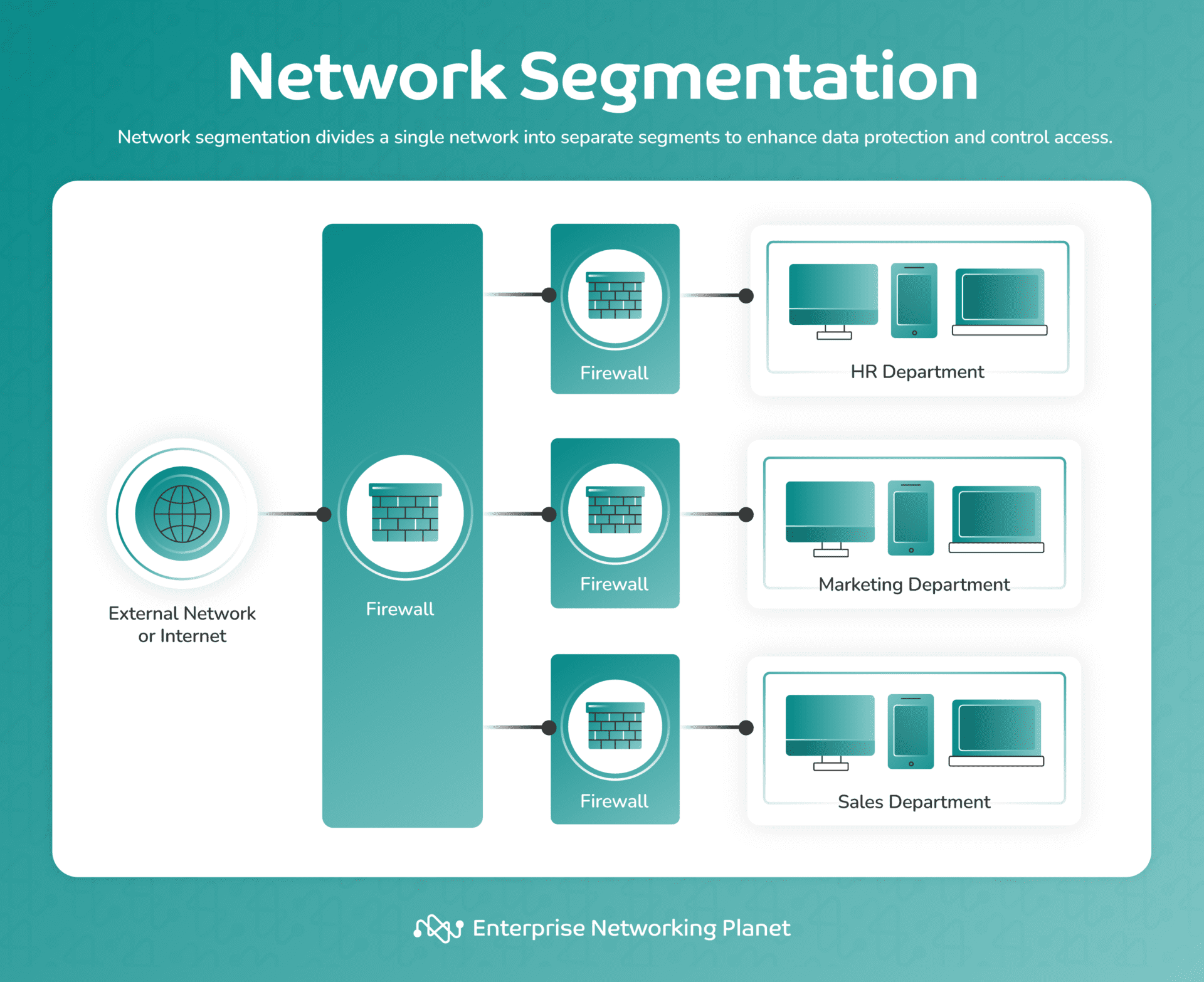
One effective way to set up a G network for data encryption is by implementing a VPN or a dedicated network. A VPN acts as a secure tunnel between your device and the internet, encrypting all data transmitted over the network. Similarly, a dedicated network isolates your device from the public internet, providing an additional layer of security for your data.
Configuring IPSec

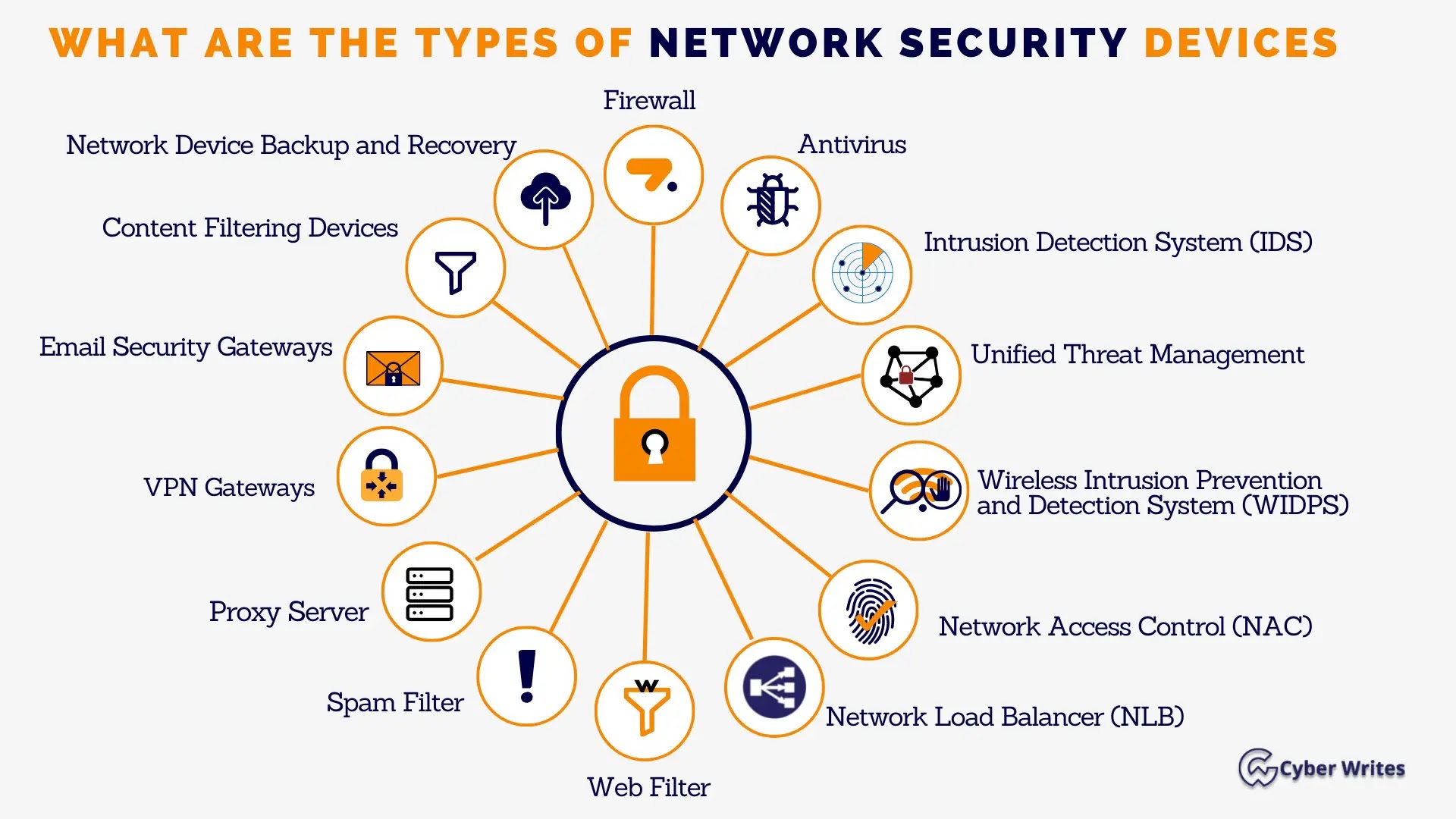
IPSec (Internet Protocol Security) is a set of communication rules or protocols that enable secure connections over a network. To set up IPSec for your G network, you'll need to configure the IPSec parameters, including encryption algorithms, authentication methods, and key exchange protocols. This process typically involves setting up an IPSec policy on your network device, such as a firewall or a VPN server.
Using Encryption Protocols
Encryption protocols, such as VPNs, TLS (Transport Layer Security), and SSL (Secure Sockets Layer), provide an additional layer of security for your data in transit. These protocols employ various encryption algorithms, such as AES, to protect your data from unauthorized access. When setting up your G network, ensure that you implement a robust encryption protocol to safeguard your data.
Implementing Network Encryption
Network encryption is essential for securing data in transit. By implementing encryption protocols and configuring IPSec, you can create a secure network that protects your data from unauthorized access. Additionally, consider implementing key management systems, such as symmetric key management, to ensure the secure exchange of encryption keys.
Key Takeaways
- Setting up a G network for data encryption is crucial for protecting sensitive information in transit.
- Understand the concept of data encryption and the various encryption algorithms, including symmetric and asymmetric encryption.
- Implement a VPN or dedicated network to isolate your device from the public internet and protect your data.
- Configure IPSec parameters, including encryption algorithms, authentication methods, and key exchange protocols.
- Use robust encryption protocols, such as VPNs, TLS, and SSL, to safeguard your data in transit.
By following these steps and implementing the necessary encryption protocols, you can create a secure G network that protects your data in transit, ensuring compliance with regulatory requirements and minimizing the risk of data breaches.


-1.webp?width=1728&height=836&name=cover%202%20(1)-1.webp)
-660.png)